The Platform Behind Every Assessment
Our proprietary platform manages the entire penetration testing lifecycle — from deal scoping to client delivery. It automates the busywork so our consultants focus on finding vulnerabilities.
End-to-End Workflow
The Complete Assessment Lifecycle
Every step tracked, audited, and optimized — from the first client conversation to remediation verification.
Deal Scoping
Built-in pricing engine with sublinear scaling across 17 assessment types. Scope engagements in minutes, not hours.
Project Setup
One-click deal-to-project conversion creates fully configured projects with assessments, targets, and personnel assignments.
Scope Definition
Define IPs, domains, URLs, and hostnames. Auto-generate tool-specific scope files for Nmap, Nuclei, and more.
Automated Scanning
Orchestrate Nmap, Nuclei, Amass, httpx, and Dehashed through production-grade Airflow pipelines with scheduled execution.
Finding Documentation
Document findings from 500+ templates with CVSS scoring, evidence management, and inline panel editing.
AI-Assisted Quality Review
In addition to human peer review, sanitized reports are reviewed by multi-model AI (Claude, GPT, Gemini) for typos, accuracy, and severity mismatches — producing a 0-100 quality score.
Peer Review
Structured 5-question reviews with threaded comments, multi-round tracking, and configurable delivery gates.
Report Generation
Generate DOCX, PDF, CSV, and web reports from a single source of truth with severity charts and professional formatting.
Secure Delivery
Time-limited tokenized download links with access tracking, expiration controls, and instant revocation.
Remediation & Retest
End-to-end retest workflow: request → assign → claim → verify → complete. Track verification evidence and status.
Client Experience
Your Client Portal
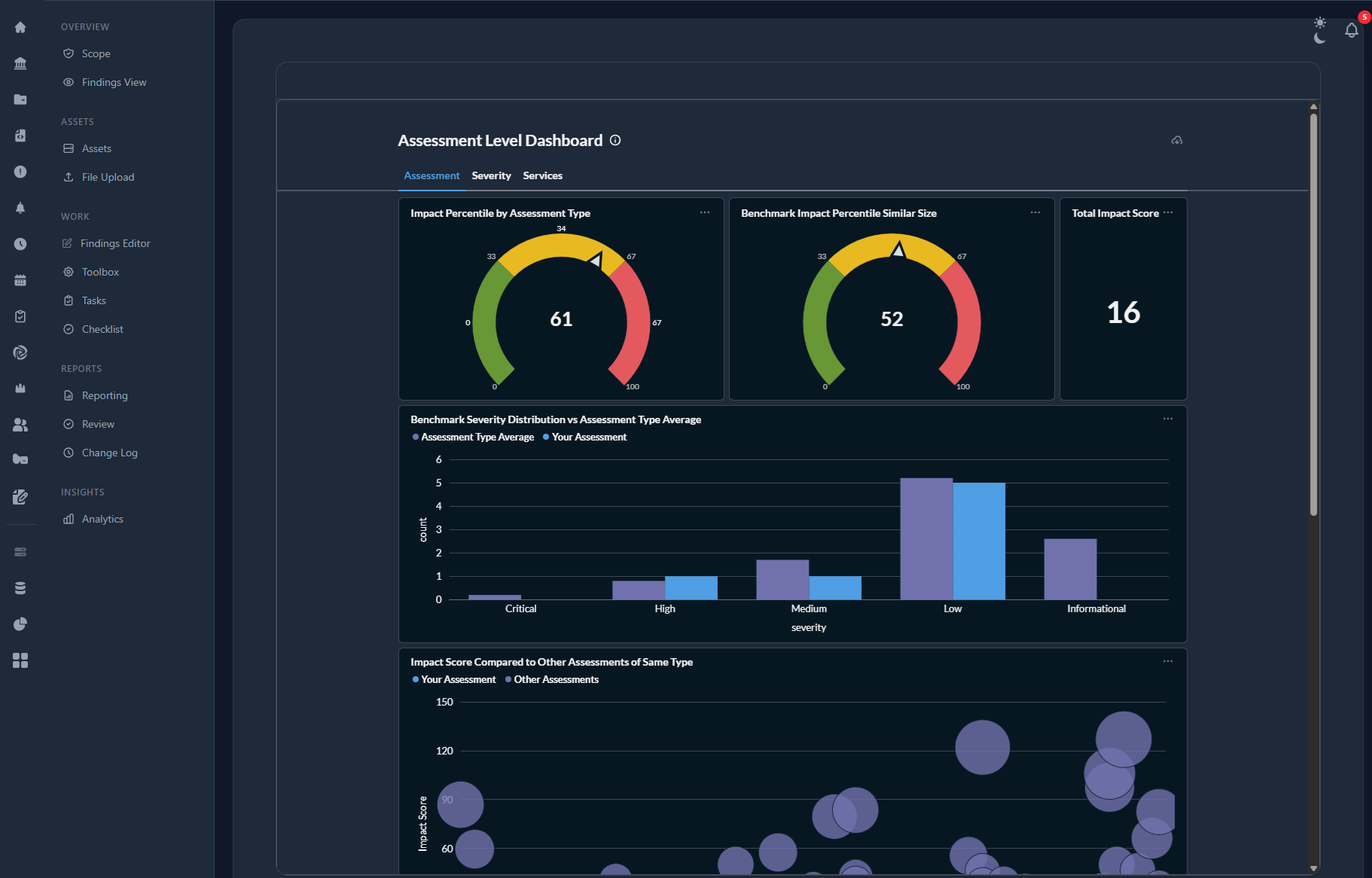
When you work with TrustFoundry, you get your own secure portal — not just a PDF. Log in with your corporate SSO to monitor testing progress, act on findings, and track your security posture over time.
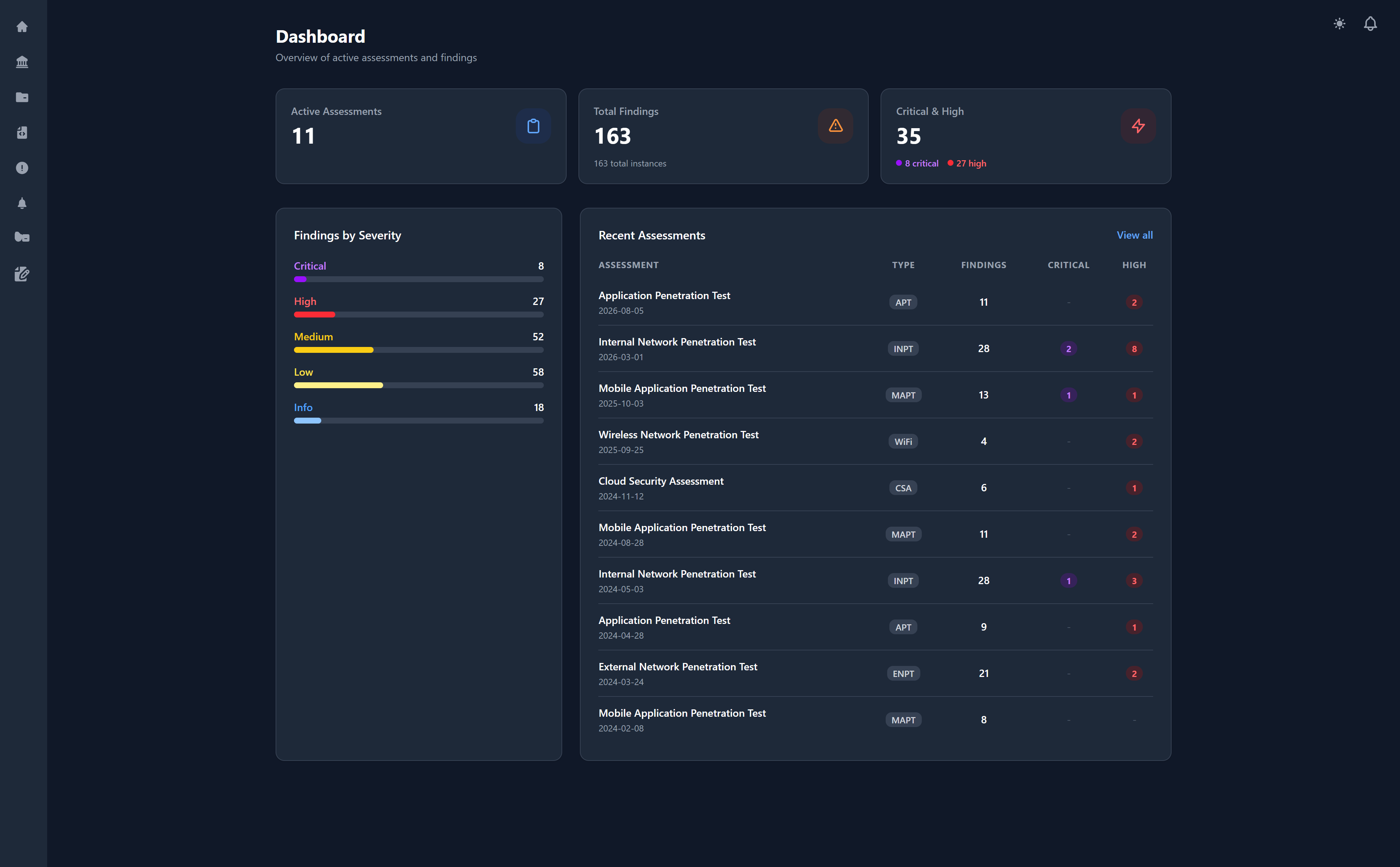
Your security dashboard — active assessments, findings by severity, and recent activity at a glance
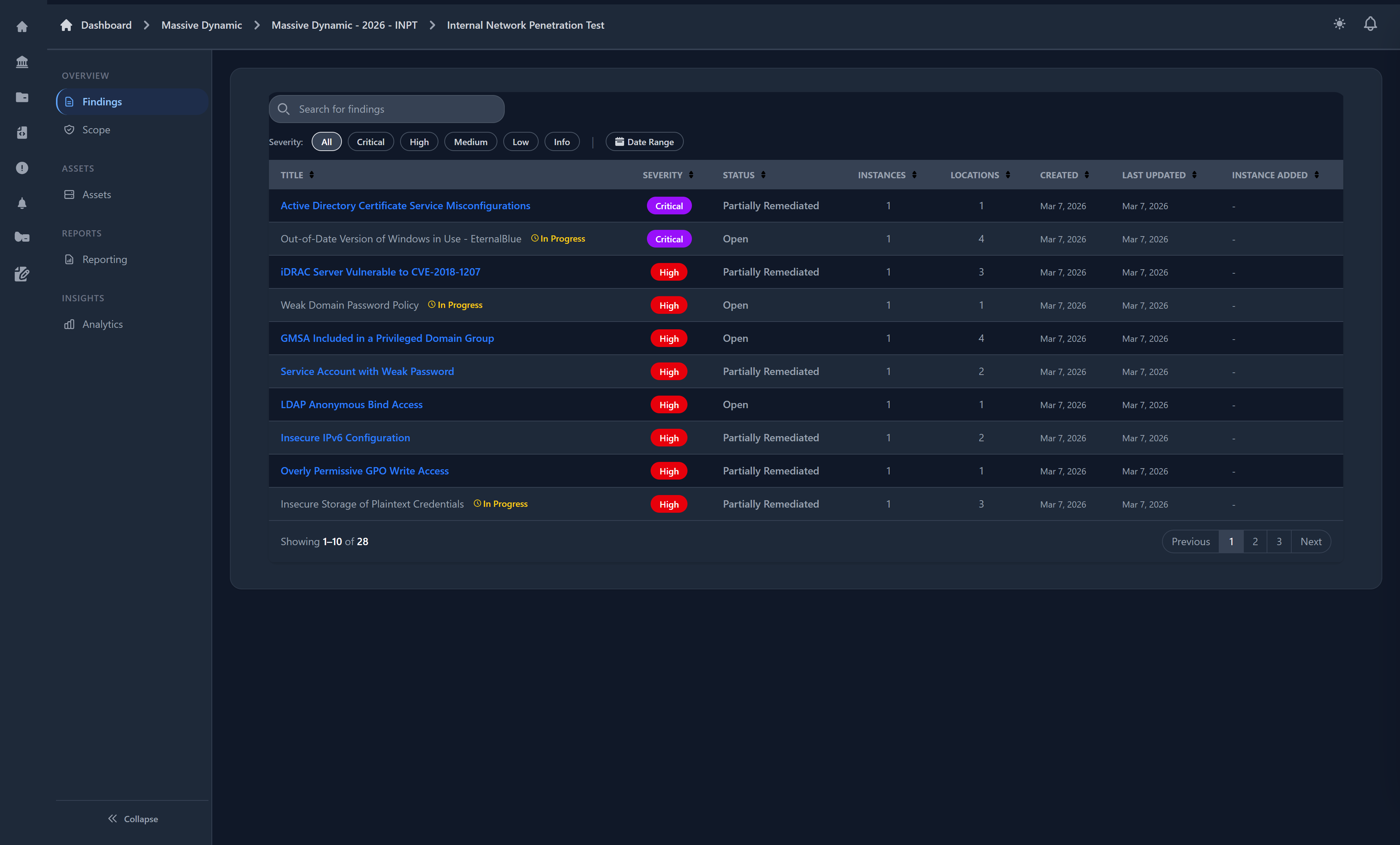
Real-Time Findings
Browse approved findings as they're discovered — don't wait for the final report to start remediating.
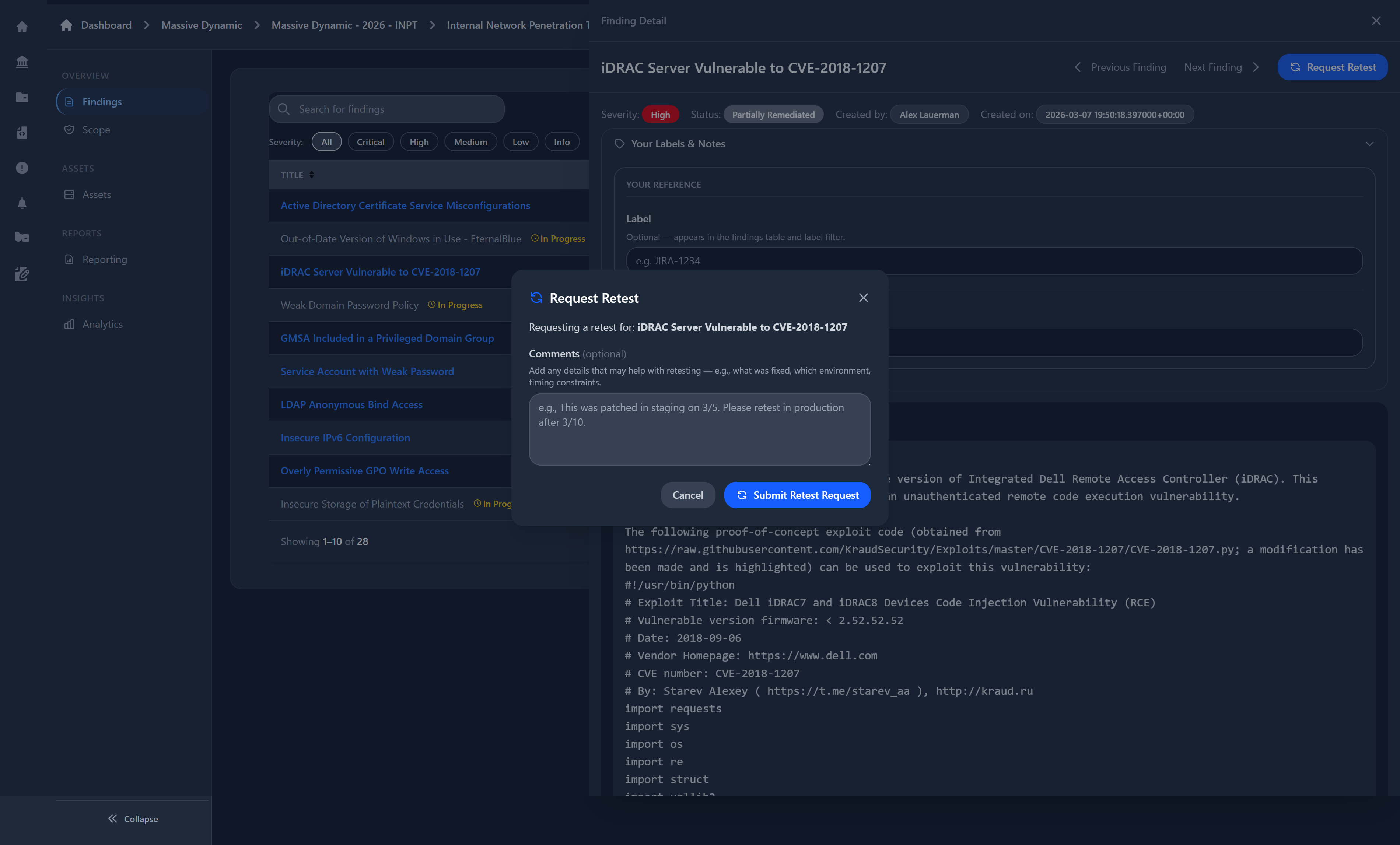
Self-Service Retesting
Request retests directly from the portal with one click. Your testing team is notified automatically.
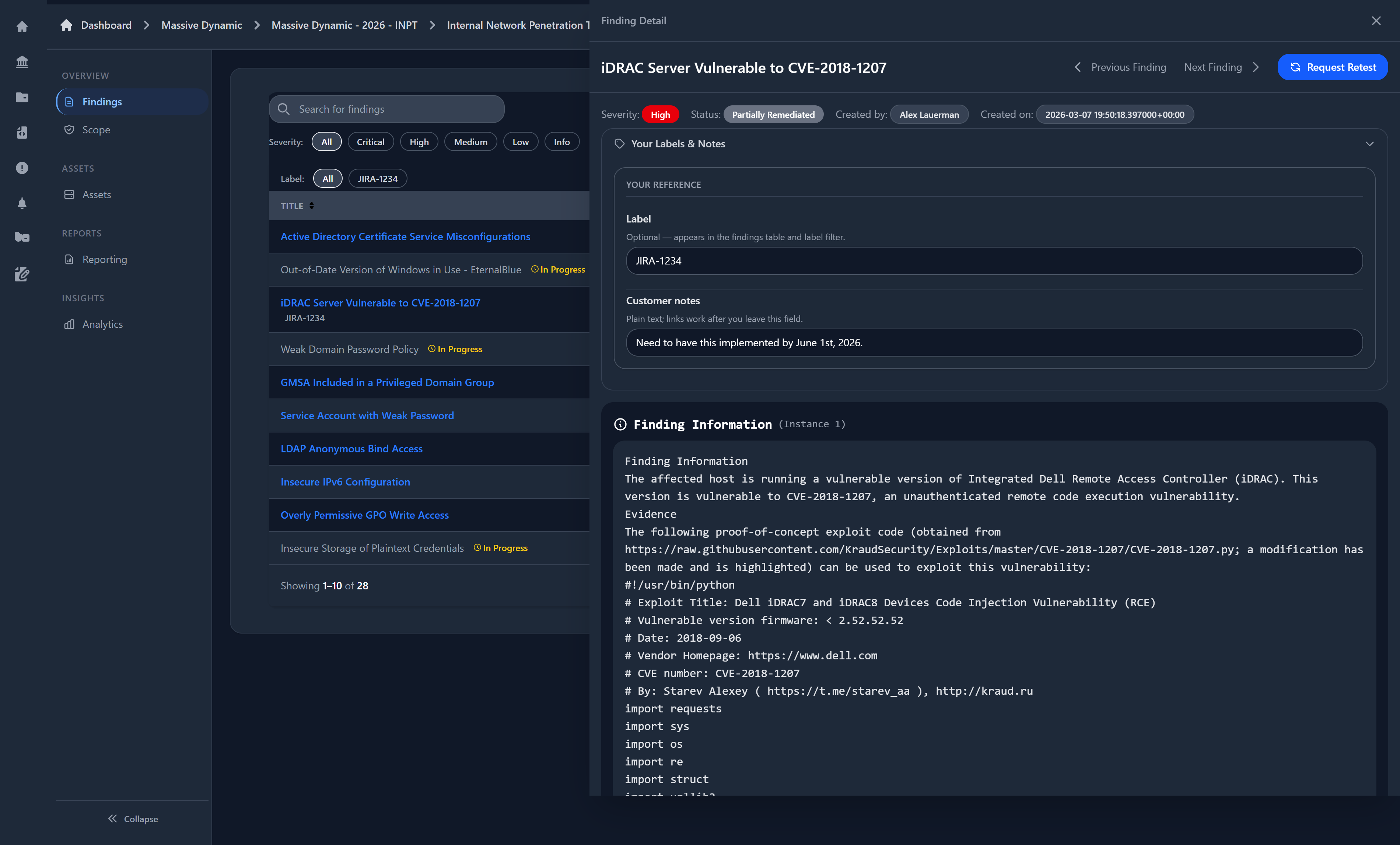
Risk Acceptance & Annotations
Formally accept risk with an auditable record. Tag findings with JIRA tickets and add notes for your team.
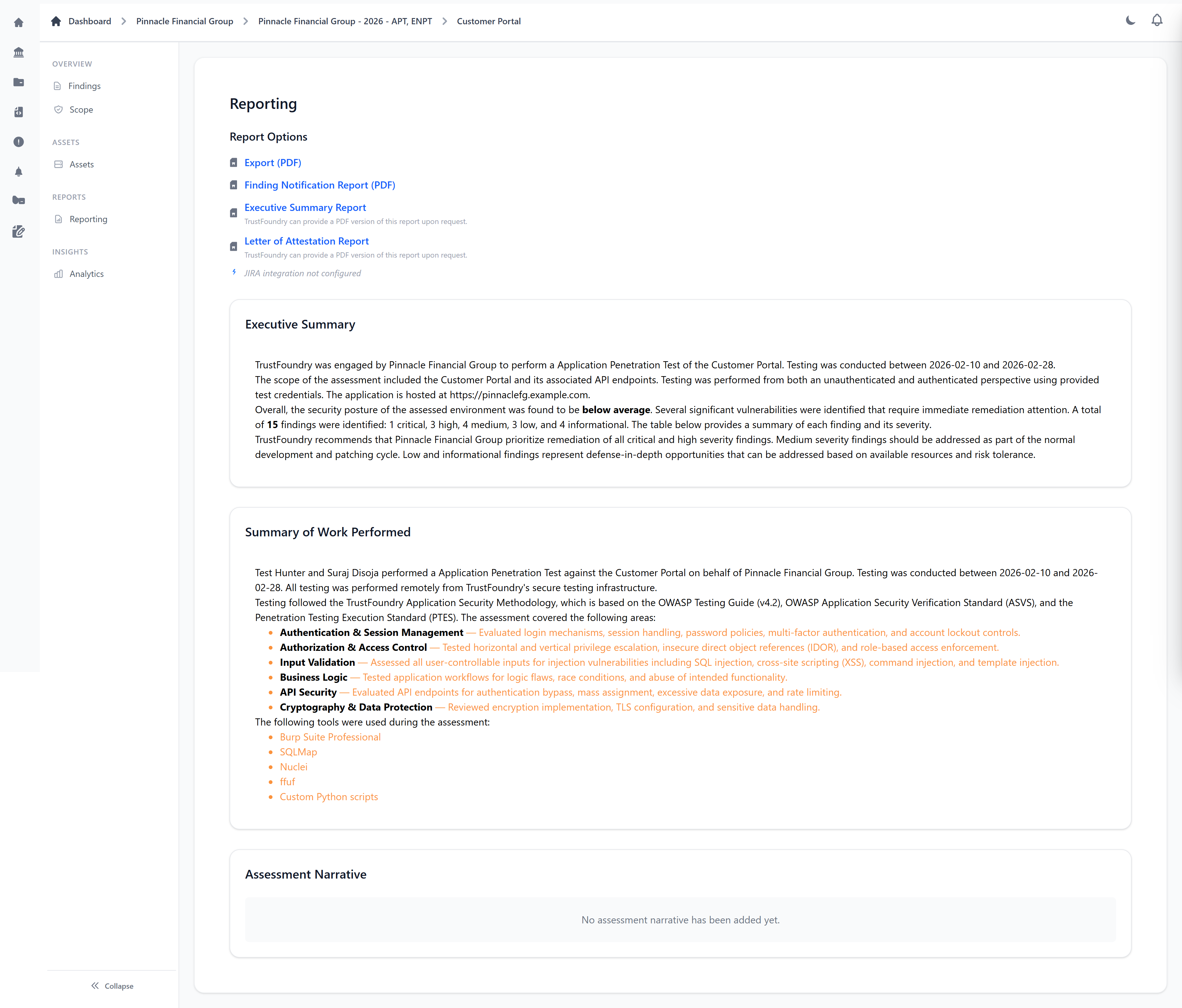
Reports & Deliverables
Download reports, executive summaries, and attestation letters directly from your portal.
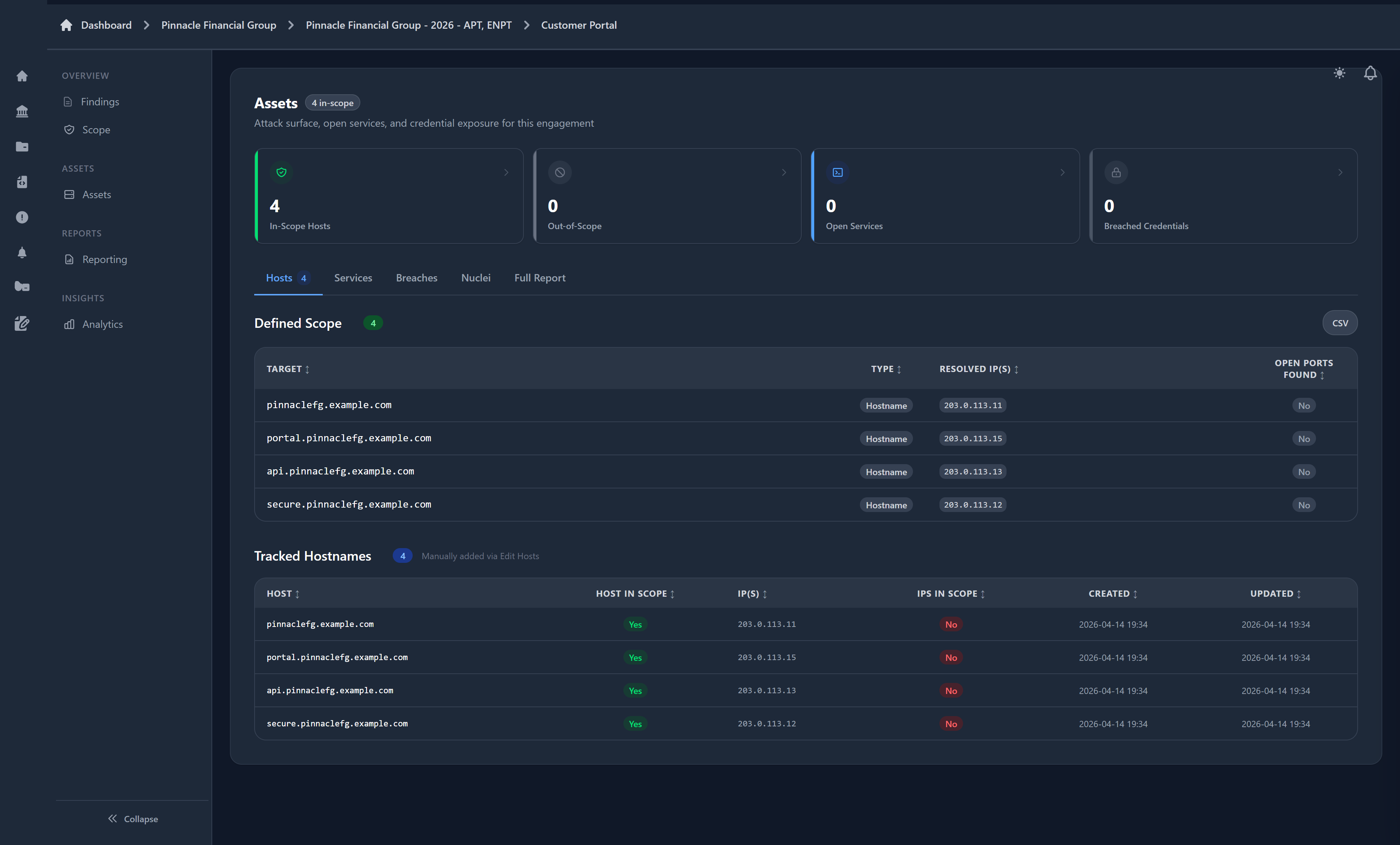
Scope & Asset Visibility
See exactly what's being tested — IPs, domains, hostnames, and all discovered services.
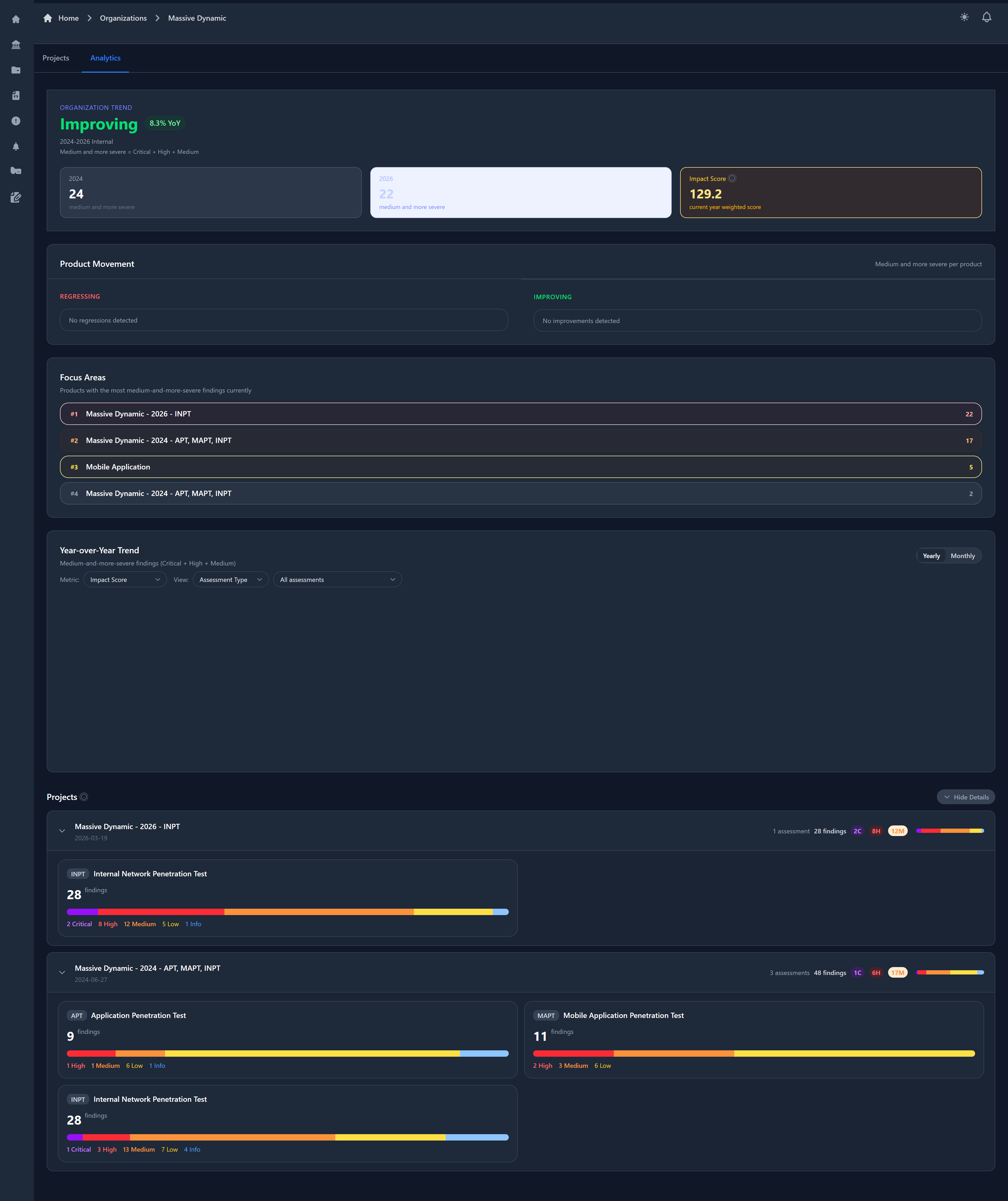
Security Analytics & Trends
Track your security posture over time with severity trends, impact scores, and year-over-year analysis.
API & AI Tool Integration
Access your findings programmatically via our REST API. Pull data into GRC platforms, internal dashboards, or AI coding tools like Claude Code.
Capabilities
462+ Features Across 35 Capability Areas
Scan Orchestration
- Nmap port scanning (top-N or custom)
- Nuclei vulnerability scanning
- Amass & Chaos subdomain enumeration
- httpx HTTP probing & tech fingerprinting
- Dehashed breach data lookup
- Scheduled daily/weekly/monthly scans
- Live WebSocket log streaming
AI-Assisted Quality Review
- Supplements human peer review — never replaces it
- Multi-model support (Claude, GPT, Gemini, Grok)
- 0-100 quality score per report
- Typo, grammar, and consistency checks
- Severity mismatch detection
- Missing content identification
- Consultant severity calibration analysis
Reporting Engine
- DOCX with severity charts & hyperlinks
- PDF export
- CSV data export
- Web-based interactive report
- Multi-assessment combined reports
- Professional formatting & templates
- DOCX round-trip import/export
Findings Knowledge Base
- 500+ curated finding templates
- Pre-written descriptions & recommendations
- CVSS 3.1 + 4.0 scoring
- Nessus plugin ID auto-mapping
- Severity ratings & categorization
- Team knowledge accumulation
- Drag-and-drop finding ordering
JIRA Integration
- One-click export to JIRA tickets
- Severity-to-priority mapping
- Evidence image attachments
- Epic creation support
- HTML-to-JIRA markup conversion
- Sync tracking for changed findings
- Per-organization JIRA configuration
Security & Compliance
- MFA with device trust
- Account lockout protection
- Role-based access control
- Field-level audit changelog
- Before/after diff tracking
- SOC 2 and PCI DSS audit support
- Secure tokenized report sharing
Smart Toolbox
- Auto-resolve IPs ↔ hostnames across scope
- Import breach data for password spraying campaigns
- Auto-generate tool-specific scope files (Nmap, Nuclei, etc.)
- Finding instances with per-instance severity & CVSS
- Nessus plugin ID → finding template auto-matching
- Bulk finding copy between assessments
- Evidence command output with syntax highlighting
Asset Inventory & Discovery
- Complete host inventory (IPs, ports, services, protocols)
- Subdomain enumeration (Amass + Chaos)
- HTTP probing with tech fingerprinting
- Service version detection across all targets
- Smart endpoint merging from multiple scans
- In-scope vs. out-of-scope host classification
- Reverse DNS tracking
Breach Data & OSINT
- Automated per-domain breach lookups (Dehashed)
- Telegram/ClickHouse breach import
- Smart deduplication of breach records
- Structured email, username, password, hash extraction
- Username enumeration across breach sources
- Dedicated breach report export
- In-app breach results browser
How We Compare
Our platform-powered approach delivers capabilities that DOCX-based firms and even dedicated pentest platforms can't match.
| Capability | TrustFoundry | DOCX-Based Firms | Other Platforms |
|---|---|---|---|
| Deal scoping & pricing engine | — | — | |
| Automated scan orchestration | — | — | |
| AI-assisted quality review | — | Partial | |
| DOCX round-trip import/export | Manual | Partial | |
| Finding instances with per-instance CVSS | — | Partial | |
| Breach data import & OSINT | — | — | |
| Auto-generated scope files for tools | — | — | |
| 500+ finding knowledge base | — | Partial | |
| Multi-round peer review workflow | — | Partial | |
| Full field-level audit changelog | — | Partial | |
| Secure tokenized report sharing | — | ||
| JIRA export with sync tracking | — | ||
| Built-in CVSS 3.1 + 4.0 scoring | — | ||
| Asset inventory & service detection | — | Partial | |
| Interactive client portal with SSO | — | ||
| Client retest requests & risk acceptance | — | Partial | |
| Interactive proposal portal | — | — | |
| E-signature (BoldSign) | — | — | |
| Assessment methodology checklists | — | Partial |
“DOCX-Based Firms” = companies using Word/Google Docs and spreadsheets. “Other Platforms” = general-purpose pentest management tools.
Integrated Tools & Services
Security tools orchestrated through production-grade pipelines, plus the integrations that tie everything together.
Security Tools
Platform Integrations
Experience the Difference
See why organizations choose TrustFoundry's platform-powered pentesting over traditional assessment firms.